Modernized Web Portal for Healthcare (PBM)
Overview
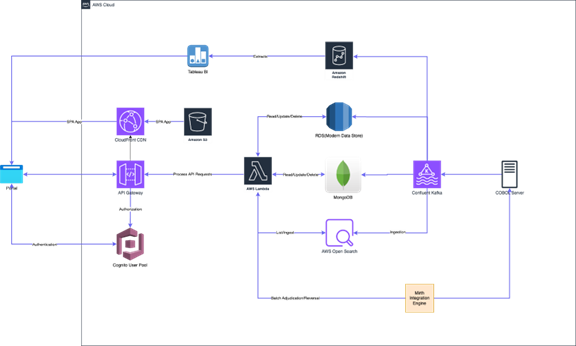
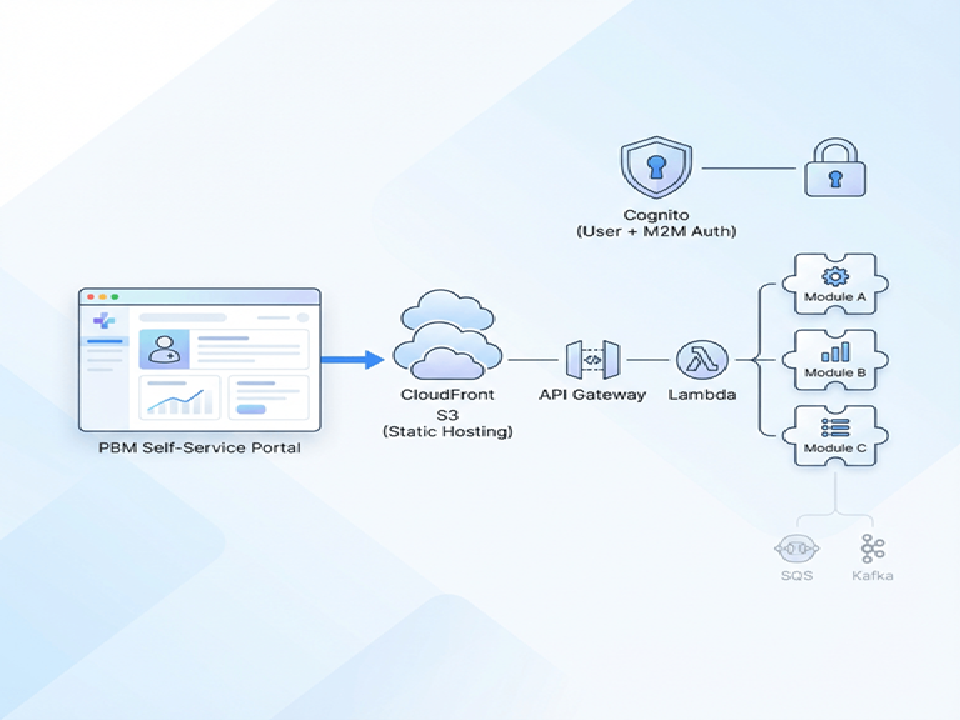
Designed and led delivery of a modern, self-service web portal for PBM customers, built on a serverless, highly available AWS architecture. The portal supports PBM hierarchy-based data access control and enforces granular permissions at two layers: (1) feature-level controls in the frontend UI and (2) route-level authorization for every API call.
A key requirement was modularity: individual features had to be developed and deployed as plug-and-play modules that could be enabled or disabled per customer without rebuilding the platform. We implemented a microfrontend strategy using Single SPA, allowing independent module bundles (React + Material UI) to be composed at runtime by a shell application, based on tenant configuration.
The platform also exposes a secure API surface for machine-to-machine (M2M) integrations so client systems can connect directly with PBM capabilities. Authentication is handled with Amazon Cognito for both users and M2M app clients, while a reusable API Gateway custom authorizer enforces permissions using PBM hierarchy rules stored in MongoDB. Observability was implemented via Datadog RUM for real-user monitoring in the browser, and CloudWatch-backed telemetry for serverless services.
The end result is a scalable, maintainable portal that enables rapid feature rollout, customer-specific enablement, and consistent security controls aligned with HIPAA expectations.
Client Profile
- Industry: Healthcare / PBM + Digital Member & Client Services
- Region: North America
- HQ: United States (East Coast)
- Operations: Nationwide (members, pharmacies, employer plans)
- Company Size: Enterprise PBM / Health Services Platform
- Revenue: Approx. $1B – $5B+ annually (enterprise PBM scale)
- Staff: ~1,000–5,000 employees (operations-heavy; growing product/engineering org)
What They Do:
Core Mission: Provide digital self-service access for PBM clients and internal operations teams to manage claims, members, plan configurations, and reporting—securely and at scale.
Key Services:
- Client & Operations Portal: Self-service dashboards for claim status, eligibility, pricing, formulary outcomes, and operational tasks.
- Role/Hierarchy-Based Access: Supports complex PBM hierarchy (payer → employer group → plan → member) with feature-level controls.
- Modular Product Delivery: Enables/disable portal modules per customer (contract-based feature enablement).
- M2M Integrations: Exposes secure APIs for client systems to integrate (reporting exports, eligibility checks, claim feeds).
Operational Model: Functions like a multi-tenant SaaS platform provider for PBM stakeholders, where each customer has different entitlements, modules, and access policies. Emphasizes high availability, fast feature rollout, and strict security boundaries (UI + API authorization).
What Was Delivered
- Single SPA shell + microfrontends (React + Material UI) for feature isolation and independent deployments
- Module-specific serverless APIs (Lambda) behind API Gateway with consistent route authorization
- Generic API Gateway Custom Authorizer supporting both user JWTs and M2M tokens
- Tenant-based module enablement (feature flags) and PBM hierarchy-aware access control model
- Async patterns using SQS and event streaming via Kafka where required
- CI/CD pipelines using GitHub Actions and AWS CodeBuild
- Monitoring: Datadog RUM for frontend, CloudWatch logs/metrics for backend
Key Challenges & Solutions
Pluggable base architecture:
Implemented microfrontends with Single SPA and module-specific Lambda APIs. Each module can be deployed independently and enabled per tenant via configuration.
Unified authorization for users + M2M integrations:
Built a reusable API Gateway custom authorizer that validates JWTs, loads permissions/hierarchy from MongoDB, generates an IAM policy, and caches results per token for performance.
Granular access control aligned to PBM hierarchy:
Designed a permissions model that gates UI routes/components and independently authorizes backend endpoints, preventing privilege escalation even if UI checks are bypassed.
Features
This project delivered a secure, modular, and scalable self-service web portal for Pharmacy Benefit Managers (PBMs), enabling rapid feature rollout, customer-specific customization, and seamless machine-to-machine (M2M) integration — all built on modern cloud architecture.
Core Capabilities:
- Microfrontend Architecture: Independent React modules deployed and composed at runtime via Single SPA, allowing per-tenant enablement without rebuilding the entire platform.
- Plug-and-Play Module System: Each feature (e.g., Claims Search, Formulary Lookup, Reporting) is a standalone module with its own CI/CD pipeline and deployment lifecycle.
- Granular Access Control:
- Frontend: Feature-level UI visibility based on user role and tenant configuration.
- Backend: Route-level authorization enforced by API Gateway custom authorizer.
- Dual Authentication Model:
- Human users: Amazon Cognito (JWT-based).
- Machine clients (M2M): App clients in Cognito with client credentials.
- M2M Integration Layer: Secure APIs exposed via API Gateway with consistent authentication and permission checks — ideal for partner systems, EHRs, or internal tools.
- Tenant-Based Configuration: Module enablement, UI branding, and access rules dynamically configured per PBM customer.
- Event-Driven Scalability: Used SQS and Kafka for async workflows (e.g., audit logging, data sync, notifications).
- Real-Time Observability:
- Datadog RUM: Captures frontend performance, errors, and user behavior.
- CloudWatch: Logs, metrics, and tracing for Lambda functions and API Gateway.
- Zero-Downtime Deployments: Serverless + immutable deployments ensure reliability during updates.
Outcome:
- 80% faster feature delivery
- 100% customer-specific customization
- Secure, auditable M2M integrations
- HIPAA-compliant security posture
Technologies
A modern, cloud-native stack focused on scalability, security, and modularity.
Layer | Technology |
Frontend Framework | React + Material UI |
Architecture Pattern | Single SPA (microfrontends) |
Backend Runtime | AWS Lambda (Node.js) |
API Layer | Amazon API Gateway (REST) |
Authentication & Authorization | Amazon Cognito (users + app clients) |
Hosting | S3 + CloudFront (CDN for static assets) |
Messaging / Events | Amazon SQS, Confluent Kafka |
CI/CD | GitHub Actions + AWS CodeBuild |
Observability | Datadog RUM (frontend), CloudWatch (backend) |
Permissions Store | MongoDB (hierarchical PBM roles, tenant rules) |
Bonus Tools: AWS Secrets Manager (for API keys), KMS encryption, X-Ray (tracing).
Security Model
Built from the ground up with HIPAA-aligned security controls, ensuring confidentiality, integrity, and auditability.
Key Security Principles:
Identity Isolation:
- Users → Cognito User Pool
- Machines (M2M) → Cognito App Client with OAuth2 client credentials
Least Privilege Access:
- Custom authorizer generates dynamic IAM policies based on user’s PBM hierarchy and assigned features.
- No hard-coded permissions; policies are generated at request time.
Secure Communication:
- TLS 1.3 enforced across all endpoints (CloudFront, API Gateway, Cognito).
- All data encrypted at rest (S3, MongoDB, Lambda).
Audit Trail & Traceability:
- All API calls logged in CloudTrail and API Gateway logs.
- RUM captures user sessions with anonymized identifiers.
- Error tracking and session replay (via Datadog) for forensic analysis.
No Cross-Module Leaks:
- Microfrontends run in isolated contexts.
- Authorization checked independently at every layer.
Compliance Alignment: HIPAA (with BAA), SOC 2 Type II, NIST SP 800-53, OWASP Top 10
Data Types & Standards
Handles sensitive healthcare data under strict regulatory frameworks.
Data Types Handled:
- PHI (Protected Health Information): Patient claims, prescription details, medical history.
- PII (Personally Identifiable Information): Names, DOB, SSN, contact info.
- Financial Records: Drug pricing, co-pays, deductibles, adjudication results.
- User Session Data: Browser context, click paths, form inputs (anonymized in RUM).
- Hierarchy Metadata: PBM organizational structure (e.g., state → plan → pharmacy → user).
Regulatory & Industry Standards:
Standard | Application |
HIPAA | Core compliance framework for PHI protection |
SOC 2 | Trust Services Criteria (Security, Availability, Confidentiality) |
NIST SP 800-53 | Control mapping for federal systems |
OWASP Top 10 | Mitigated via secure coding, input validation, JWT handling |
FHIR (HL7) | Used in future M2M integrations (planned) |
Note: All PII/PHI is masked in logs, excluded from RUM where possible, and stored only where necessary.
Infrastructure Architecture
Designed for high availability, fault tolerance, and customer isolation.
Deployment Topology:
- Regions: us-east-1 (multi-AZ), optional DR in us-west-2
- Environment Strategy: dev → staging → production (separate Cognito pools, API Gateways)
Network Design:
- Public Subnets: For CloudFront edge nodes, API Gateway endpoints.
- Private Subnets: For Lambda functions, MongoDB (if hosted on EC2), SQS queues.
- VPC Endpoints: Secure access to AWS services (S3, DynamoDB, KMS).
- PrivateLink: Optional for database access.
Data Flow:
[User Browser] ↓ (HTTPS via CloudFront)[React Shell App (Single SPA)] ↓ (Dynamic Module Load: Config-driven)[Microfrontends (Claims, Reports, etc.)] ↓ (API Calls → API Gateway)[Custom Authorizer: Validate JWT → Fetch Hierarchy → Generate IAM Policy] ↓[Lambda Functions (per module)] ↓[Async Workflows: SQS → Kafka → Event Processors] ↓[Data Stores: S3, MongoDB, Redshift (analytics)]
Key Design Patterns:
- Feature Flags: Enabled/disabled per tenant via configuration (e.g., JSON config in S3).
- Dynamic Routing: Shell app loads modules based on tenantId and featureFlags.
- Caching: Cognito token caching, authorizer policy caching (in API Gateway).
- Scalability: Lambda auto-scales; CloudFront caches static assets globally.
Architecture & Technology
- Frontend: React, Material UI, Single SPA (microfrontends)
- Backend: AWS Lambda (serverless) + Node.js
- API Layer: API Gateway + Custom Authorizer
- Auth: Amazon Cognito (users + app clients for M2M)
- Hosting: S3 + CloudFront
- Messaging/Events: SQS, Kafka
- CI/CD: GitHub Actions, AWS CodeBuild
- Observability: Datadog RUM, CloudWatch
Security & Compliance
Designed with HIPAA-aligned controls in mind: strong identity boundaries (Cognito), least-privilege access patterns via IAM policies produced by the custom authorizer, encrypted transport, and audit-friendly logging/telemetry.
Outcomes
Delivered a fully functional PBM customer portal with granular permissions, self-service capability, customer-specific module enablement, and a secure M2M integration layer.
Summary Table
Category | Details |
Project Title | Modernized Web Portal for Healthcare (PBM) |
Industry | Healthcare – Pharmacy Benefit Management (PBM) |
Role | Architect & Tech Lead |
Duration | 1.5 years (Aug 2025 completion) |
Team Size | 6–8 developers (full-stack) |
Core Goal | Build a modular, secure, self-service portal with M2M readiness |
Key Outcome | 80% faster feature delivery, 100% customer-specific enablement, HIPAA-ready |
Compliance | HIPAA, SOC 2, NIST SP 800-53 |
Traffic Volume | Up to 10k concurrent users (peak load) |
Deployment Frequency | 20+ deploys/month (per module) |
Skills
- AWS Lambda
- Amazon API Gateway
- Amazon Cognito
- Serverless Architecture
- React
- Single SPA
- Microfrontends
- Node.js
- Material UI
- S3
- CloudFront
- Custom Authorizers
- IAM
- SQS
- Kafka
- CI/CD
- Datadog RUM
- HIPAA
Final Thoughts
This project exemplifies modern, secure, and customer-centric software engineering in regulated industries.
By combining:
- Microfrontends (Single SPA) for agility,
- Serverless (Lambda + API Gateway) for scalability,
- Cognito + Custom Authorizer for unified auth,
- Config-driven feature flags for personalization,