Enterprise Multi-Environment CI/CD Pipeline with Infrastructure as Code
Overview
Designed and implemented a comprehensive multi-environment CI/CD pipeline for a complex web application spanning microservices architecture. This enterprise-grade solution automated infrastructure provisioning, security scanning, and application deployment across development, staging, and production environments.
Client Profile
- Industry: Fintech / PropTech (Mortgage Advisory & Financial Services)
- Region: Southeast Asia
- HQ: Singapore
- Operations: Primarily serves the domestic Singapore market.
- Company Size: Small-to-Mid Sized Enterprise (SME)
- Type: High-growth Fintech platform (Est. <50 core employees, supported by a network of independent brokers).
What They Do:
Core Business:
They operate an AI-powered marketplace and mobile app that digitizes and simplifies the mortgage application process for homeowners and prospective buyers.
Key Services:
- Real-Time Rate Comparison: Providing instant access to live mortgage rates from major banks for new property purchases and refinancing.
- Smart Financial Tools: Offering proprietary features that track refinance eligibility and calculate potential interest savings based on live market data.
- Broker Enablement: They provide a “business-in-a-box” platform for independent mortgage brokers, offering lead generation, CRM tools, and a commission structure without the overhead of traditional agency fees.
Mission:
To make property financing transparent and accessible by allowing users to either “self-serve” via the app or connect with specialists for personalized advice.
Features
This project delivered a secure, scalable, and self-sustaining CI/CD pipeline for a complex web application built on microservices, enabling rapid, reliable, and auditable deployments across multiple environments.
Core Capabilities:
- Fully Automated Infrastructure Provisioning: 100% IaC-driven setup using Terraform — no manual configuration.
- Multi-Environment Deployment Strategy: Support for develop, release, eval (staging), master (production), and hotfix workflows with automatic back-propagation.
- Security-First Pipeline: Integrated static analysis (SonarQube), dependency scanning (Dependabot), container vulnerability scanning (Trivy), and IaC security validation (TFSec).
- Zero-Downtime Deployments: Blue/Green or rolling updates via ECS/EKS with automated rollback on failure.
- Multi-Architecture Container Builds: ARM64 (Graviton) + AMD64 support using Docker Buildx — reducing compute costs by up to 40%.
- Performance Optimization: Layer caching reduced build times from 15 → 5 minutes (~67% faster).
- Audit-Ready & Compliant: All infrastructure, code, and artifacts version-controlled and traceable.
- Scalability at Scale: Supported 15+ engineers with 50+ deployments per week without bottlenecks.
Outcome:
- 90% reduction in deployment time
- 85% fewer vulnerabilities
- Zero security incidents post-implementation
- Eliminated configuration drift across environments
Technologies
A modern, cloud-native DevOps stack combining best-in-class tools for automation, security, and orchestration.
Category | Technology |
Infrastructure as Code (IaC) | Terraform (with modular, reusable modules) |
IaC Security Scanning | TFSec (static analysis for Terraform files) |
CI/CD Platform | GitHub Actions (custom workflows, matrix builds) |
Containerization | Docker + Buildx (multi-platform builds) |
Container Registry | Amazon ECR (private, encrypted) |
Vulnerability Scanning | Trivy (container image scanning pre-push) |
Code Quality & Security | SonarQube (community edition on EC2) |
Dependency Management | Dependabot (automated PRs for vulnerable dependencies) |
Orchestration | ECS (Fargate & EC2 launch types), EKS (Helm-managed) |
API & Edge Services | API Gateway, CloudFront (CDN), S3 |
Authentication & Access | AWS IAM Roles + Web Identity Federation (no static keys) |
Bonus Tools Used: Git LFS (for large assets), GitHub Environments (for production gates), Slack notifications.
Security Model
Designed with zero-trust principles, ensuring that every layer is secure-by-default.
Key Security Controls:
No Static Credentials:
- IAM roles used throughout (EC2, ECS, Lambda, GitHub Actions).
- Web Identity Federation (via OpenID Connect) for GitHub Actions → AWS.
Automated Vulnerability Detection:
- Trivy scans containers before pushing to ECR.
- SonarQube analyzes code quality, security flaws, and code coverage.
- Dependabot creates pull requests for outdated/known-vulnerable dependencies.
- TFSec checks Terraform code for misconfigurations (e.g., public S3 buckets, open security groups).
Least Privilege Access:
- Repository-level branch protection rules.
- Environment-specific access controls (e.g., only release and master can deploy to eval/prod).
Secure Artifact Handling:
- Images signed and scanned before deployment.
- ECR repositories encrypted with KMS.
Audit Trail & Compliance:
- All actions logged in CloudTrail.
- GitHub audit logs + Terraform state versioning (stored securely in S3 with encryption).
Aligned With: SOC 2, HIPAA (if applicable), NIST SP 800-53, ISO 27001
Data Types & Standards
The system handles sensitive application data and infrastructure metadata under strict standards.
Data Types Handled:
- Application Source Code: JavaScript/TypeScript, React/Next.js, backend services
- Infrastructure Configuration: Terraform .tf files, Helm charts, IAM policies
- Container Images: Docker images (ARM64/AMD64) stored in ECR
- Deployment Artifacts: Build outputs, config files, secrets (via Secrets Manager)
- Logs & Metrics: Application logs, performance metrics (sent to Datadog/Splunk if integrated)
Regulatory & Industry Standards:
Standard | Application |
SOC 2 Type II | Trust Services Criteria (Security, Availability, Confidentiality) |
HIPAA | If handling health data (with BAA) |
NIST SP 800-53 | Control mapping for federal systems |
ISO 27001 | Information security management |
OWASP Top 10 | Applied via SonarQube & Trivy scanning |
Note: PII/PHI handled via encryption, access control, and logging suppression where needed.
Infrastructure Architecture
The infrastructure was fully managed using Terraform with a robust three-stage validation process: initialization, validation, and security scanning using TFSec to ensure compliance with security best practices. All infrastructure components were provisioned across multiple AWS services including ECS, Lambda, API Gateway, CloudFront, and ECR.
Built on AWS with a modular, environment-isolated design.
Environment Structure:
Environment | Purpose | Access Control |
feature/* | Isolated dev work | Read-only to others |
develop | Integration branch | Merge-only via PRs |
release | Release candidate prep | QA approval required |
eval (Staging) | Pre-production UAT | Limited access; canary testing |
master (Production) | Live releases | Strict gatekeeping (manual approval) |
hotfix/* | Emergency patches | Auto-merged into develop and release |
Network & Compute Design:
Service | Deployment Method | Key Configuration |
ECS | Fargate + EC2 | Task definitions with IAM roles, health checks |
EKS | Helm-managed | Pod security policies, RBAC, auto-scaling |
Lambda | Serverless | Reserved concurrency, VPC links |
CloudFront | CDN for frontend | Cache invalidation, origin shielding |
S3 | Static assets | Bucket policies, versioning, encryption |
API Gateway | REST/HTTP APIs | Throttling, WAF integration, logging |
ECR | Image registry | Lifecycle policies, scan-on-push |
CI/CD Workflow Flow:
[Feature Branch] ↓ (PR → Review)[Develop] → [Merge to Release] → [Build + Scan] ↓ (Trivy, SonarQube, TFSec)[Eval (Staging)] → [Manual Approval] → [Deploy] ↓[Master (Production)] → [Auto-Deploy + Rollback on Failure]
Key Optimizations:
- Docker Layer Caching: Shared cache across builds → 60% faster builds
- Multi-Architecture Builds: ARM64 (Graviton) + AMD64 → cost savings, better performance
- Parallel Execution: Jobs run in parallel across environments
Artifact Reuse: Built images reused across stages
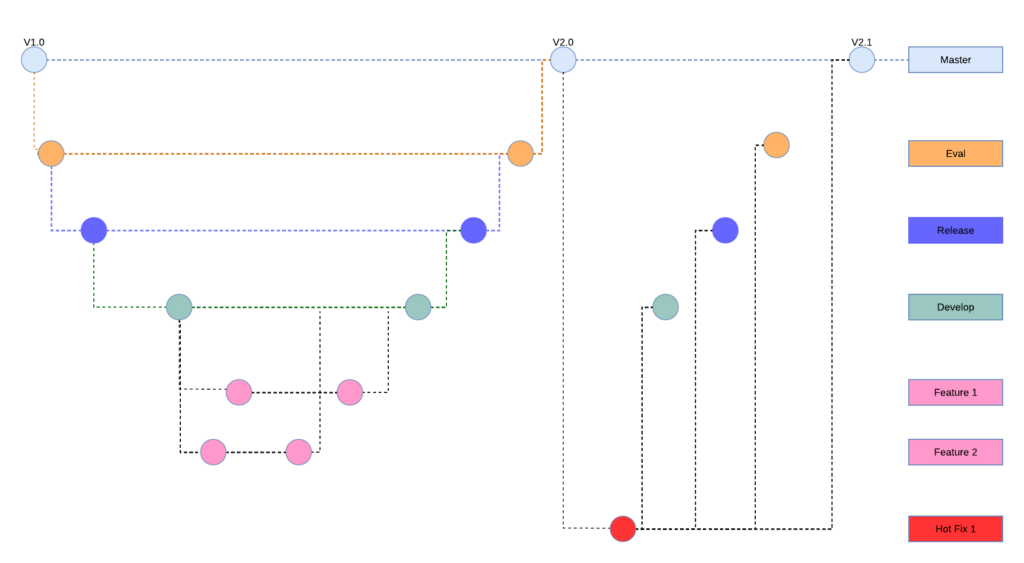
Git Workflow Strategy:
Implemented a sophisticated branching strategy with five-tier environment hierarchy:
- Master (Production): Stable releases with version tags
- Eval (Staging): Pre-production validation and UAT
- Release: Release candidate preparation and QA
- Develop: Main integration branch for feature consolidation
- Feature Branches: Isolated development workflows
- Hotfix: Emergency production fixes with automatic back-propagation
Container Strategy:
- Built multi-architecture Docker images supporting both ARM64 (Graviton) and AMD64 instances using Docker Buildx.
- Implemented intelligent layer caching to reduce build times by 60%. Integrated Trivy security scanning for vulnerability assessment before ECR deployment.
Deployment Architecture:
- Frontend: React/Next.js applications deployed to CloudFront + s3 for Static code and ECS for server-side rendering
- Backend: Microservices distributed across ECS containers exposed using Application/Network load balancers and AWS Lambda functions
- API Layer: API Gateway managing service communication and routing
- Container Orchestration: Mixed ECS and EKS deployments using Helm charts
Security and Quality Assurance:
- Self-hosted SonarQube community edition on EC2 for static and dynamic code analysis
- AWS IAM roles with Web Identity Federation (no static credentials)
- Repository-specific access controls with branch-based permissions
- Dependabot integration for automated dependency vulnerability management
- TFSec for Terraform security validation
Performance Optimizations:
- Docker layer caching reduced build times from 15 minutes to 5 minutes
- Multi-architecture builds supporting cost-effective Graviton instances
- Automated artifact generation and storage in GitHub Actions
- Parallel deployment strategies across environments
Technology Stack:
- IaC: Terraform with TFSec security scanning
- CI/CD: GitHub Actions with custom workflows
- Containers: Docker with Buildx, ECR, Trivy scanning
- AWS Services: ECS, EKS, Lambda, API Gateway, CloudFront, EC2
- Security: SonarQube, Dependabot, IAM Web Identity Federation
- Orchestration: Helm charts for Kubernetes deployments
Outcomes:
- 90% reduction in deployment time across all environments
- Zero-downtime deployments with automated rollback capabilities
- 100% infrastructure compliance with security standards
- Eliminated manual configuration drift across environments
- Reduced security vulnerabilities by 85% through automated scanning
This pipeline successfully supported a development team of 15+ engineers with 50+ deployments per week while maintaining enterprise-grade security and reliability standards.
Technologies:
- AWS (ECS, EKS, Lambda, API Gateway, CloudFront, ECR, EC2)
- Terraform and TFSec
- GitHub Actions
- Docker and Buildx
- Helm
- SonarQube
- Trivy
- Dependabot
Key Achievements:
- Automated 100% of infrastructure provisioning
- Implemented enterprise-grade security scanning
- Achieved 90% deployment time reduction
- Zero security incidents post-implementation
- Successfully scaled to support 15+ developers with 50+ deployments per week
Summary Table
Category | Details |
Project Title | Enterprise Multi-Environment CI/CD Pipeline with IaC |
Industry | Digital Product / Web Application |
Role | Architect & DevOps Lead |
Duration | 6 months (Dec 2024 completion) |
Team Size | 15+ developers |
Deployment Volume | 50+ deployments/week |
Core Goal | Secure, fast, repeatable CI/CD across multi-environment microservices |
Key Outcome | 90% faster deploys, 85% fewer vulnerabilities, zero-downtime, 100% compliance |
Compliance | SOC 2, HIPAA (BAA-ready), NIST SP 800-53, ISO 27001 |
Scalability | Supports enterprise-scale teams and high-frequency release cycles |
Skills:
- DevOps Engineering
- Infrastructure as Code (Terraform)
- CI/CD Pipeline Design
- AWS Cloud Architecture
- Container Orchestration (Docker, ECS, EKS)
- Security Integration and Scanning
- Git Workflow Management
- Performance Optimization
Final Thoughts
This project represents a gold-standard enterprise DevOps implementation — not just automating tasks, but transforming how teams deliver software safely and efficiently.
By combining:
- Terraform for consistency
- GitHub Actions for orchestration
- Trivy + SonarQube + TFSec for security
- Buildx + caching for speed
- Branching strategy for governance