AWS Control Tower Multi-Account Architecture & Governance

Overview
Designed and implemented a comprehensive AWS multi-account architecture leveraging AWS Organizations and Control Tower for a healthcare technology organization. The solution established a secure, compliant, and scalable cloud foundation supporting multiple business units while preparing for enterprise-wide cloud migration.
Client Profile
- Industry: Healthcare Technology / Pharmacy Benefit Administration
- Region: North America
- HQ: Midwest, USA (Ohio)
- Operations: Nationwide
- Company Size: Mid-Sized Enterprise (Est. 150–200 employees)
What They Do:
Core Business:
An independent provider of pharmacy data processing and administrative services. They build backend technology that allows Health Plans, Hospital Systems, and Hospice organizations to manage their own prescription drug programs.
Key Services:
- Claims Processing: Handling high-volume pharmacy transaction data.
- 340B Administration: Managing federal drug pricing compliance for hospitals and clinics.
- Data Transparency: Unlike traditional competitors, they utilize a “pass-through” model, granting their clients full ownership and 24/7 access to their own operational data.
Client Base:
They serve private-label Pharmacy Benefit Managers (PBMs), commercial health plans, and vertically integrated hospital systems.
Key Features
This project focuses on Governance, Security, and Scalability for a healthcare environment.
- Multi-Account Governance: A centralized “Landing Zone” managing 18 distinct accounts organized into 4 Organizational Units (OUs) for separation of concerns.
- Centralized Network Inspection: A dedicated Inspection VPC that filters all traffic (East-West, North-South, and Ingress) using AWS Network Firewall to ensure no malicious traffic enters or leaves the network.
- Hybrid Connectivity: Secure connection between on-premises data centers and AWS using Site-to-Site VPN and Transit Gateway, preparing for future Direct Connect integration.
- Automated Account Provisioning: Uses “Account Factory” to create new accounts with standard configurations in hours rather than days.
- Identity Federation: Single Sign-On (SSO) implemented by integrating Microsoft Entra ID (Azure AD) with AWS IAM Identity Center.
- FinOps & Cost Visibility: Centralized cost dashboards, anomaly detection, and mandatory tagging strategies to track spending across business units ($1,070 – $1,585/month baseline).
- Disaster Recovery (DR): Multi-region strategy with defined RPO/RTO targets and cross-region replication for critical workloads.
Technologies Stack
The solution leverages a wide array of AWS native services and external integrations.
Category | Services & Tools Used |
Core Management | AWS Organizations, AWS Control Tower, AWS Service Catalog |
Networking | AWS Transit Gateway, AWS Site-to-Site VPN, Amazon Route 53 (Resolver), VPC, NAT Gateways |
Security (Network) | AWS Network Firewall (Stateful/Stateless rules), VPC Flow Logs |
Security (Governance) | AWS GuardDuty, Security Hub, Detective, Config, CloudTrail, KMS, IAM Identity Center |
DevOps & Automation | AWS CodePipeline, AWS CodeBuild, AWS Systems Manager, CloudFormation, EC2 Image Builder |
Monitoring | Amazon CloudWatch, AWS Cost Explorer |
Integrations | Microsoft Entra ID (Azure AD), Git Repositories |
Security Model
Because this is a Healthcare Technology project, the security model is strict, following a Defense-in-Depth approach.
Perimeter Security (Centralized Inspection):
- Traffic is routed through a specific Inspection VPC.
- AWS Network Firewall applies stateful rules (domain filtering, protocol inspection) and stateless rules (DDoS protection, packet inspection).
Identity & Access Management (IAM):
- Least Privilege Access: Enforced across all accounts.
- SSO: Users log in via Microsoft Entra ID.
Guardrails & Policies:
- Service Control Policies (SCPs): Applied at the OU level (Security, Shared, Prod, Non-Prod) to prevent unauthorized actions (e.g., stopping logging, leaving the organization).
- Compliance Rules: AWS Config rules enforce specific configurations (e.g., encryption must be on).
Data Protection:
- Encryption: Enforced At-Rest (using KMS) and In-Transit.
- Isolation: Production environments are strictly isolated from Non-Production environments.
Data Types & Standards
The architecture is designed to handle sensitive healthcare information and meet regulatory audits.
Compliance Standards:
- HIPAA: The architecture supports Health Insurance Portability and Accountability Act requirements (data privacy/security).
- SOC2: Security controls support Service Organization Control Type 2 reporting.
- AWS Well-Architected Framework: The design aligns with AWS best practices.
Data Types:
- PHI (Protected Health Information): Handled within the isolated “Production” and “Application” accounts.
- Audit & Log Data: Centralized storage of CloudTrail logs, VPC Flow Logs, and Config history in the “Log Archive” account (immutable storage).
- Threat Intelligence Data: Integrated via AWS Managed Threat Intelligence.
Infrastructure Overview
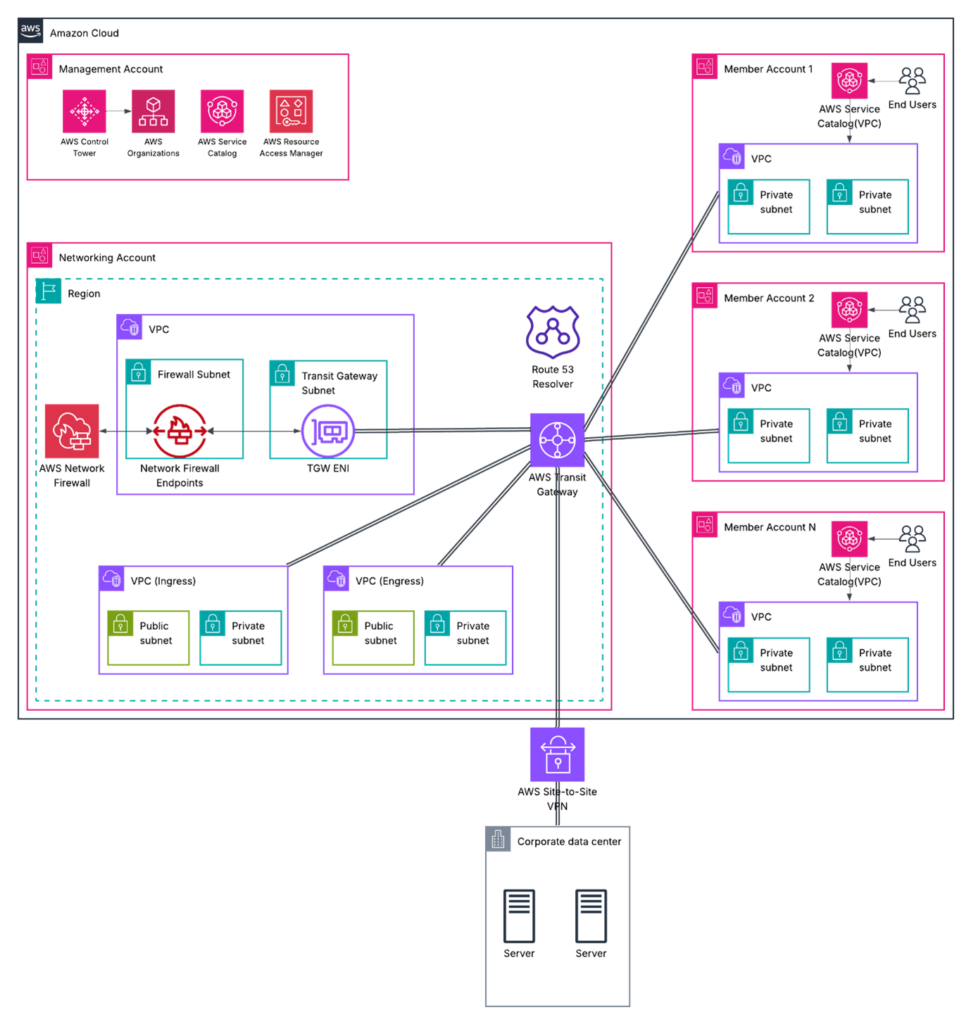
The physical and logical layout of the cloud environment.
Account Structure (18 Accounts Total):
- Network Security OU: Log Archive, Audit, Security Services.
- Shared Services OU: Shared Services, Networking (Hub), Deployment (CI/CD).
- Production OU: Primary Prod, Application A & B Prod, DR accounts, Legacy staging.
- Non-Production OU: Dev and QA environments.
Topology:
- Hub-and-Spoke: The “Networking Account” acts as the Hub (via Transit Gateway), and all other accounts (Spokes) connect to it.
- Routing: Custom route tables ensure traffic flows through the Inspection VPC before reaching its destination.
Compute & Storage:
- Standardized Golden AMIs (Amazon Machine Images) created via Image Builder for EC2 instances.
- Centralized S3 buckets for logging.
Business Challenge
The organization required a robust cloud governance framework to:
- Manage multiple business applications across isolated environments
- Ensure HIPAA compliance and healthcare data security
- Enable development, QA, and production segregation
- Prepare for migration of on-premises workloads to AWS
- Implement centralized cost management and visibility
- Establish secure hybrid connectivity for gradual migration
Solution Architecture
Multi-Account Structure
Designed a 18-account architecture organized across 4 Organizational Units:
Security OU (3 accounts)
- Log Archive Account – Centralized logging repository
- Audit Account – Security monitoring and compliance
- Security Services Account – Threat detection and automation
Shared Services OU (3 accounts)
- Shared Services Account – Common enterprise services
- Networking Account – Hub for connectivity and routing
- Deployment Account – CI/CD pipeline orchestration
Production OU (6 accounts)
- Primary Production & DR – Core business workloads
- Application A Production – Dedicated application environment
- Application B Production & DR – Isolated healthcare application
- Legacy Account – Existing workload migration staging
Non-Production OU (6 accounts)
- Separate Dev/QA environments for all applications
- Cost-optimized development infrastructure
Key Technical Implementations
Governance & Security
- Implemented Service Control Policies (SCPs) across all OUs for compliance enforcement
- Integrated Microsoft Entra ID with AWS IAM Identity Center for SSO
- Deployed AWS GuardDuty, Security Hub, and Detective for threat detection
- Established CloudTrail organization trail and AWS Config for audit compliance
- Enforced encryption at rest and in transit across all accounts
Networking & Connectivity
- Designed Transit Gateway hub-and-spoke architecture
- Implemented Site-to-Site VPN for hybrid connectivity
- Centralized NAT Gateways and Internet Gateway management
- Configured Route 53 Resolver for hybrid DNS resolution
- Prepared infrastructure for future AWS Direct Connect integration
Network Architecture: Centralized Inspection
Implemented a Centralized Inspection Architecture to provide unified security inspection for all network traffic across the multi-account environment. This design ensures consistent security posture and simplified management of network security controls.
Architecture Components
Inspection VPC (in Networking Account)
- Dedicated VPC acting as the central inspection point
- AWS Network Firewall deployed in multiple Availability Zones
- Inspection subnets for stateful traffic filtering
- Firewall endpoints for high availability
Traffic Flow Design
- East-West Traffic: Inter-VPC communication routed through inspection VPC
- North-South Traffic: Internet-bound traffic inspected before egress
- Ingress Traffic: External requests inspected before reaching workloads
- Hybrid Traffic: On-premises connectivity secured through centralized inspection
AWS Network Firewall Implementation
Stateful Rule Groups
- Domain-based filtering for malicious sites and threat intelligence
- Protocol-specific inspection (HTTP/HTTPS/DNS)
- Custom application-layer rules
- Integration with AWS Managed Threat Intelligence
Stateless Rule Groups
- Fast-path filtering for known traffic patterns
- Capacity-based packet inspection
- Priority-based rule evaluation
- DDoS protection rules
Logging and Monitoring
- Flow logs sent to Log Archive Account
- Alert logs for security event detection
- Integration with CloudWatch for real-time monitoring
- Security Hub integration for centralized findings
Transit Gateway Integration
Route Table Configuration
- Spoke VPCs route traffic to inspection VPC via Transit Gateway
- Inspection VPC routes traffic back to destination via TGW
- Segregated routing for production and non-production environments
- Blackhole routes for known malicious destinations
Traffic Segmentation
- Production OU traffic isolated from Non-Production
- Security OU has read-only access for monitoring
- Shared Services accessible with controlled policies
- Legacy account traffic monitored during migration
Key Benefits
Security
- Single point of inspection for all network traffic
- Consistent security policies across all accounts
- Centralized threat prevention and detection
- Reduced attack surface with controlled egress
Operational Efficiency
- Simplified security rule management
- Centralized logging and compliance reporting
- Reduced operational overhead
- Automated threat intelligence updates
Cost Optimization
- Shared Network Firewall resources across accounts
- Reduced data transfer costs through optimized routing
- Eliminated redundant security appliances
- Predictable network security costs
Compliance
- Centralized audit trail for all network communications
- Enforced security policies at network level
- Simplified compliance reporting
- Support for regulatory requirements (HIPAA, SOC2)
Automation & Operations
- Leveraged Account Factory for standardized account provisioning
- Created golden AMI pipeline using EC2 Image Builder
- Implemented centralized patch management with Systems Manager
- Established cross-account CI/CD pipelines with AWS CodePipeline
- Deployed automated cost anomaly detection and budget alerts
Disaster Recovery
- Designed multi-region DR strategy with RPO/RTO targets
- Implemented cross-region replication for critical workloads
- Configured Route 53 health checks and failover routing
- Established quarterly DR testing procedures
Technical Deliverables
Documentation
- Comprehensive architecture blueprint (18 pages)
- Service Control Policy definitions for each OU
- Landing Zone Governance Model
- Account-wise component specifications
- Migration and connectivity strategy
- Baseline cost analysis
Infrastructure Components
- 18 AWS accounts with standardized configurations
- Multi-OU organizational structure with guardrails
- Centralized logging and monitoring infrastructure
- Cross-account IAM roles and permissions
- Network architecture with TGW and VPN
- Security tooling across all environments
Governance Framework
- 4 distinct SCP sets tailored to each OU
- Mandatory tagging policies for cost allocation
- Compliance rules for Config and Security Hub
- Automated remediation workflows
- Cost optimization and FinOps dashboard
Business Impact
Security & Compliance
- Achieved centralized security monitoring across 18 accounts
- Implemented automated threat detection and incident response
- Established audit-ready logging and compliance reporting
- Enforced encryption and access controls organization-wide
Operational Efficiency
- Reduced account provisioning time from days to hours
- Standardized CI/CD pipelines across all environments
- Automated patch management and configuration compliance
- Centralized monitoring and alerting
Cost Management
- Established visibility across all accounts ($1,070 – $1,585/month baseline)
- Implemented tagging strategy for cost allocation
- Created FinOps dashboard for ongoing optimization
- Projected cost savings through Savings Plans and Reserved Instances
Scalability & Future-Readiness
- Built foundation for enterprise cloud migration
- Designed hybrid connectivity for phased migration approach
- Enabled rapid onboarding of new teams and projects
- Established scalable networking architecture
Technologies & Services Used
Core AWS Services
- AWS Organizations & Control Tower
- AWS IAM Identity Center
- AWS Transit Gateway
- AWS Site-to-Site VPN
- Amazon Route 53
Security & Compliance
- AWS GuardDuty
- AWS Security Hub
- AWS Detective
- AWS Config
- AWS CloudTrail
- AWS KMS
Monitoring & Logging
- Amazon CloudWatch
- AWS CloudTrail
- VPC Flow Logs
- AWS Cost Explorer
Automation & DevOps
- AWS Service Catalog (Account Factory)
- AWS CodePipeline & CodeBuild
- AWS Systems Manager
- AWS CloudFormation
- AWS EC2 Image Builder
Integration
- Microsoft Entra ID (Azure AD)
- Git Repository Integration
Project Highlights
Architecture Excellence
- Designed solution aligned with AWS Well-Architected Framework
- Implemented least-privilege access across all accounts
- Created separation of duties between security, networking, and workloads
- Established disaster recovery with cross-region capabilities
Migration Strategy
- Developed 3-phase migration roadmap from on-premises to AWS
- Designed hybrid connectivity with redundancy and failover
- Planned for AWS Database Migration Service and Application Migration Service integration
- Documented migration approach minimizing business disruption
Cost Optimization
- Provided detailed baseline cost analysis for infrastructure
- Designed cost allocation strategy using mandatory tagging
- Implemented automated cost anomaly detection
- Created framework for ongoing FinOps practices
Key Competencies Demonstrated
- Cloud Architecture: Multi-account AWS design at enterprise scale
- Security Engineering: Comprehensive security and compliance framework
- Network Design: Hybrid connectivity and hub-and-spoke architecture
- Governance: Policy-driven controls using SCPs and guardrails
- Automation: Infrastructure as Code and CI/CD implementation
- Cost Management: FinOps practices and optimization strategies
- Migration Planning: Phased enterprise cloud migration strategy
- Documentation: Comprehensive technical blueprints and runbooks
Project Artifacts
- Architecture diagrams and reference documentation
- Service Control Policy templates
- Landing Zone governance model
- Account provisioning standards
- Network design specifications
- Cost baseline analysis
- Migration strategy documentation
Contact & Collaboration
This project demonstrates expertise in designing and implementing enterprise-scale AWS architectures with strong emphasis on security, compliance, and operational excellence. Available for similar cloud transformation initiatives.
Core Strengths:
- AWS Solutions Architecture
- Multi-Account Governance
- Cloud Security & Compliance
- Hybrid Cloud Connectivity
- Cost Optimization
- Enterprise Migration Planning