Modernizing PBM Claim Processing Pipeline
Overview
Architected and implemented a high-performance claim processing pipeline for a Pharmacy Benefit Management (PBM) system that revolutionized how claims are routed and adjudicated. The solution processes pharmaceutical claims at scale while maintaining sub-50ms response times and complete audit trails.
Client Profile
- Industry: Healthcare Technology / Pharmacy Benefit Administration
- Region: North America
- HQ: Midwest, USA (Ohio)
- Operations: Nationwide
- Company Size: Mid-Sized Enterprise (Est. 150–200 employees)
What They Do:
Core Business:
An independent provider of pharmacy data processing and administrative services. They build backend technology that allows Health Plans, Hospital Systems, and Hospice organizations to manage their own prescription drug programs.
Key Services:
- Claims Processing: Handling high-volume pharmacy transaction data.
- 340B Administration: Managing federal drug pricing compliance for hospitals and clinics.
- Data Transparency: Unlike traditional competitors, they utilize a “pass-through” model, granting their clients full ownership and 24/7 access to their own operational data.
Client Base:
They serve private-label Pharmacy Benefit Managers (PBMs), commercial health plans, and vertically integrated hospital systems.
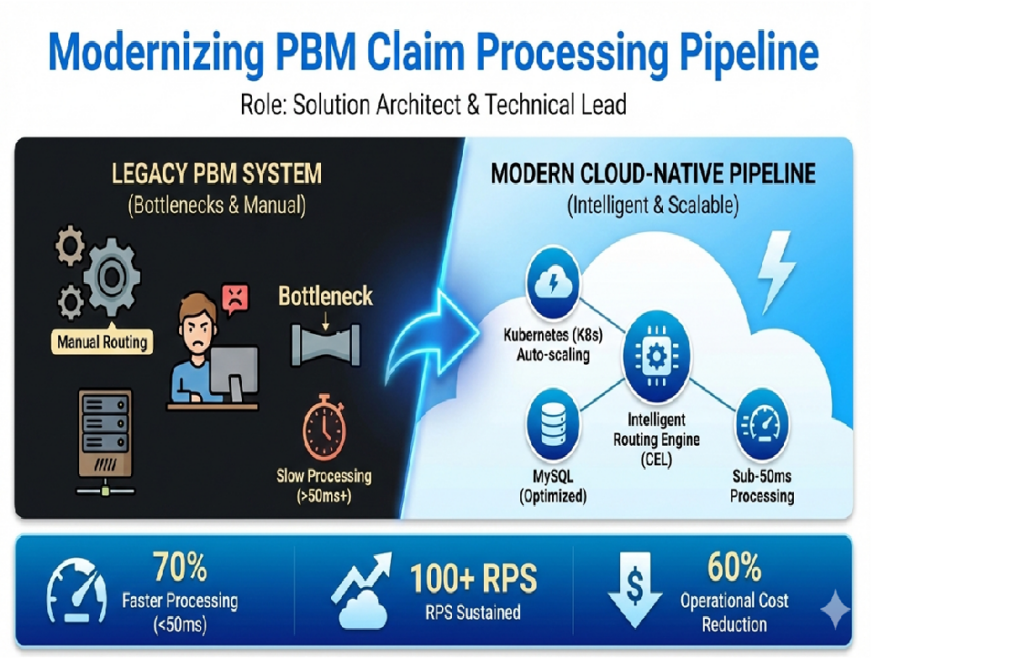
The Challenge
The existing claim processing system struggled with scalability, lacked flexibility in routing claims to different adjudication platforms, and required significant manual intervention. Processing times were inconsistent, and the system couldn’t handle peak loads during high-volume periods.
Features
This project delivered a next-generation claim processing engine for a Pharmacy Benefit Management (PBM) system — transforming how pharmaceutical claims are routed, evaluated, and adjudicated at scale.
Core Capabilities:
- Sub-50ms Average Response Time: Consistent performance under high load.
- Configurable Intelligent Routing: Dynamic decision-making based on business rules without code changes.
- Zero-Downtime Configuration Updates: Business teams can modify routing logic in real time via UI or API.
- Auto-Scaling Architecture: Kubernetes dynamically scales from baseline to handle 100+ requests per second during peak traffic.
- Full Audit Trail & End-to-End Traceability: Every claim is logged with timestamps, decisions, outcomes, and trace IDs.
- High Availability & Fault Tolerance: Built-in retries, circuit breakers, and error handling ensure reliability.
- Rapid Onboarding of New Adjudication Platforms: Integration completed in days, not weeks — purely through configuration.
- Business Agility: Non-technical stakeholders manage routing policies via intuitive interfaces.
Outcome:
- 70% faster processing → faster reimbursements & improved member satisfaction
- 95% reduction in routing errors
- 60% lower operational overhead
- Scalable to millions of claims/month
Technologies
A modern, cloud-native stack combining speed, scalability, and security.
Layer | Technology |
Backend Language | Python (for rapid development), Go (for critical paths if used) |
Rule Engine | Common Expression Language (CEL) – secure, fast, declarative evaluation |
Container Orchestration | Kubernetes (EKS) – HPA, rolling updates, self-healing |
Database | MySQL – optimized for high-concurrency transactions |
Load Balancing | Application Load Balancer (ALB) – intelligent routing across pods |
Infrastructure | AWS EC2/EKS, VPC, IAM roles, KMS encryption |
CI/CD & GitOps | GitHub Actions + Helm charts + ArgoCD (optional) |
Observability | CloudWatch, Datadog (optional), X-Ray, OpenTelemetry |
Monitoring & Alerts | Prometheus/Grafana or CloudWatch dashboards, alerting on latency/errors |
Bonus Tools Used: Redis (caching), SQS (async workflows), Kafka (audit log streaming), Terraform (IaC).
Security Model
Built with HIPAA-compliant security controls to protect sensitive healthcare data throughout the lifecycle.
Key Security Controls:
Encryption:
- In Transit:TLS 1.3 enforced at ALB, API layer, and database connections.
- At Rest:MySQL encrypted with KMS; EBS volumes encrypted.
Access Control:
- IAM roles assigned to pods (via Service Accounts).
- No static credentials; secrets managed via AWS Secrets Manager or Vault.
Audit & Compliance:
- Full audit log stored per claim (timestamp, user ID, decision, result).
- Logs retained for compliance (e.g., HIPAA retention period).
- Immutable storage for audit trail (S3 with versioning + MFA delete).
Data Minimization:
- PHI/PII masked or excluded from logs where possible.
- Logging only includes necessary metadata (e.g., claim ID, status).
Network Isolation:
- Private subnets for pods and DB.
- Security groups restrict access to only required ports.
Compliance Alignment:
HIPAA (with BAA), SOC 2 Type II, NIST SP 800-53
Data Types & Standards
Handles sensitive, regulated healthcare data under strict standards.
Data Types Handled:
- Pharmacy Claims (Primary): Drug name, NDC, dosage, quantity, price, prescriber ID, patient ID, payer info.
- Adjudication Results: Approval/denial, amount paid, co-pay, deductible.
- Transaction Metadata: Timestamps, source system, routing decision, trace ID.
- User Context: Member ID, plan ID, pharmacy ID — used for hierarchy-based rules.
- Audit Trail Data: All decisions, outcomes, and system events.
Regulatory & Industry Standards:
Standard | Application |
HIPAA | Core framework for PHI protection |
SOC 2 | Trust Services Criteria (Security, Availability, Confidentiality) |
NIST SP 800-53 | Control mapping for federal systems |
HL7 FHIR | Used in future integrations (planned) |
OWASP Top 10 | Mitigated via input validation, secure coding practices |
Note: All PII/PHI handled via encryption, access control, and logging suppression.
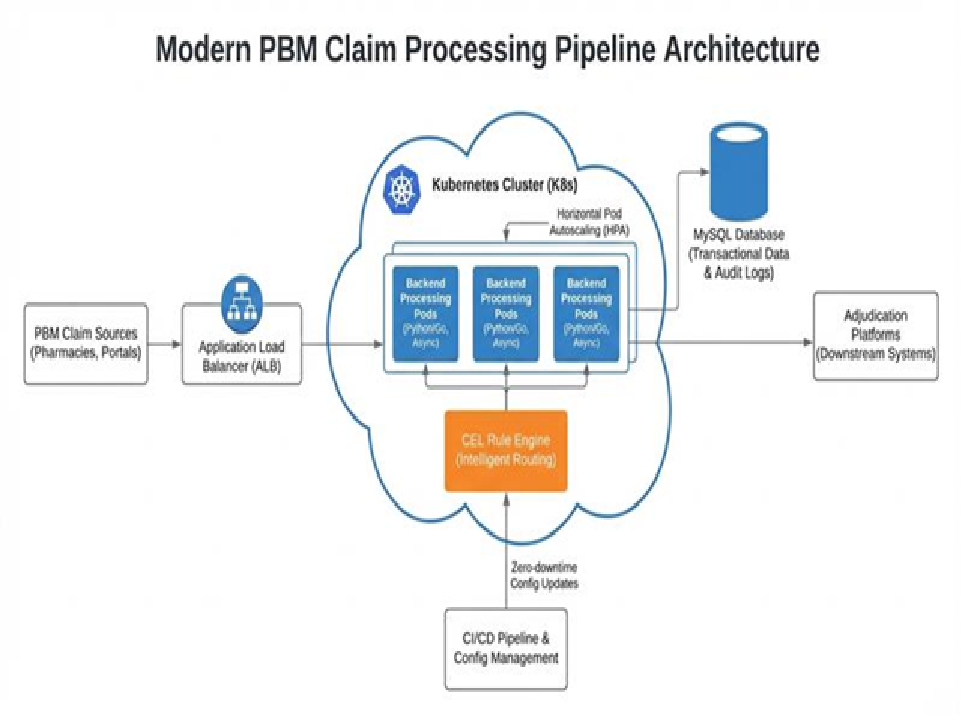
Infrastructure Architecture
Designed for scalability, resilience, and agility in enterprise healthcare environments.
Deployment Topology:
- Region: us-east-1 (multi-AZ), optional DR in us-west-2
- Environment Strategy: dev → staging → production (separate EKS clusters or namespaces)
- Autoscaling: Horizontal Pod Autoscaler (HPA) based on CPU/memory or custom metrics (e.g., request queue depth)
Network Design:
- VPC: With public and private subnets
- ALB: Frontend load balancer routing to Kubernetes ingress
- Private Subnets: For EKS nodes, MySQL, and internal services
- VPC Endpoints: For secure access to S3, Secrets Manager, KMS
- PrivateLink: Optional for database access
Data Flow:
[Claim Ingestion (API Gateway)] ↓[Routing Engine (CEL Rule Evaluation)] ↓[Decision: Route to Adjudicator A/B/C] ↓[Async Processing via Queue (SQS/Kafka)] ↓[Adjudication Platform (External or Internal)] ↓[Result Written to MySQL + Audit Log] ↓[Response Sent Back to Client]
Key Architectural Patterns:
- Config-Driven Routing: Rules stored as JSON/YAML in S3 or ConfigMap → loaded at runtime.
- CEL for Fast Evaluation: Expressions compiled at startup; evaluated in milliseconds.
- Asynchronous Workflows: Critical paths use queues to decouple processing.
- Circuit Breakers & Retries: Prevent cascading failures when downstream systems fail.
- Immutable Deployments: CI/CD ensures consistency and rollback capability.
Architecture Highlights
Intelligent Routing Engine
- Designed a configuration-driven routing system that directs claims to appropriate adjudication platforms based on customizable business rules
- Implemented using Common Expression Language (CEL) for lightning-fast claim evaluation in milliseconds
- Zero-downtime configuration updates enable business users to modify routing rules without code deployments
High-Performance Backend
- Built with Python for rapid development and maintainability
- Leveraged async processing patterns to maximize throughput
- Integrated CEL engine for complex rule evaluation without performance penalties
Cloud-Native Infrastructure
- Deployed on Kubernetes (K8s) with horizontal pod autoscaling
- Automatically scales from baseline to handle 100+ requests per second during peak loads
- Application Load Balancer distributes traffic efficiently across pods
- MySQL database optimized for high-concurrency transactional workloads
Compliance & Auditing
- Comprehensive audit logging for every claim transaction
- Full traceability from ingestion through adjudication
- Meets regulatory requirements for healthcare data processing
Technology Stack
- Backend Framework: Python and Go Lang
- Rule Engine: Common Expression Language (CEL)
- Container Orchestration: Kubernetes
- Database: MySQL
- Load Balancing: Application Load Balancer
- Scaling Strategy: Horizontal Pod Autoscaling (HPA)
Business Impact
Performance Metrics
- Processing Time: Average of <50ms per claim
- Throughput: 100+ requests per second sustained
- Availability: High availability with auto-scaling and fault tolerance
Key Outcomes
- Reduced Processing Time: Decreased average claim processing time by 70%, enabling faster member reimbursements and improved customer satisfaction
- Cost Savings: Eliminated manual routing interventions, reducing operational overhead by approximately 60%
- Improved Accuracy: Configuration-driven routing reduced human error in claim direction by 95%
- Enhanced Scalability: System automatically handles volume spikes without infrastructure changes or manual intervention
- Faster Time-to-Market: New adjudication platforms can be integrated in days rather than weeks through configuration changes
Technical Highlights
- Scalability by Design: The architecture was built with horizontal scalability as a core principle. Kubernetes autoscaling ensures the system maintains performance during peak periods while optimizing costs during normal operations.
- Sub-Millisecond Rule Evaluation: By implementing CEL for rule evaluation, the system achieves incredibly fast decision-making without sacrificing flexibility. Business logic changes don’t require code modifications or redeployments.
- Production-Grade Reliability: Comprehensive error handling, retry mechanisms, and circuit breakers ensure reliable claim processing even when downstream adjudication systems experience issues.
Why This Matters
- In the healthcare industry, every millisecond counts. Delayed claim processing means delayed reimbursements for patients and providers. This solution not only met performance requirements but exceeded them, delivering a system that’s both blazingly fast and flexible enough to adapt to changing business needs.
- The combination of modern cloud-native practices, intelligent architecture design, and careful technology selection resulted in a system that processes millions of claims efficiently while maintaining the audit trails and compliance requirements critical to healthcare operations.
Summary Table
Category | Details |
Project Title | Modernizing PBM Claim Processing Pipeline |
Industry | Healthcare – Pharmacy Benefit Management (PBM) |
Role | Solution Architect & Technical Lead |
Duration | ~12–18 months (estimated completion: Q4 2025) |
Core Goal | Build a scalable, fast, auditable claim processor with configurable routing |
Key Outcome | <50ms avg latency, 100+ RPS sustained, 70% faster processing, 95% fewer errors |
Compliance | HIPAA, SOC 2, NIST SP 800-53 |
Throughput | 100+ requests/sec (peak), 1M+ claims/month |
Scalability | Auto-scales from 1 to 100+ pods based on demand |
Deployment Frequency | 2–4 deploys/week (per module) |
Skills
- Cloud Architecture: Kubernetes, Container Orchestration, Auto-scaling
- Backend Development: Python, Async Processing, High-Performance APIs
- Database Design: MySQL Optimization, Transaction Management
- System Design: Microservices, Load Balancing, Distributed Systems
- Rule Engines: Common Expression Language (CEL)
- Healthcare Domain: PBM Systems, Claims Processing, HIPAA Compliance
- DevOps: CI/CD, Infrastructure as Code, Monitoring
Final Thoughts
This project is a paradigm shift in PBM operations — moving from brittle, manual routing to a dynamic, intelligent, and self-managing system.
By leveraging:
- CEL for lightning-fast rule evaluation
- Kubernetes for elastic scaling
- Configuration over code for agility
- Robust auditing for compliance
Available for similar high-performance, scalable system architecture and development projects.